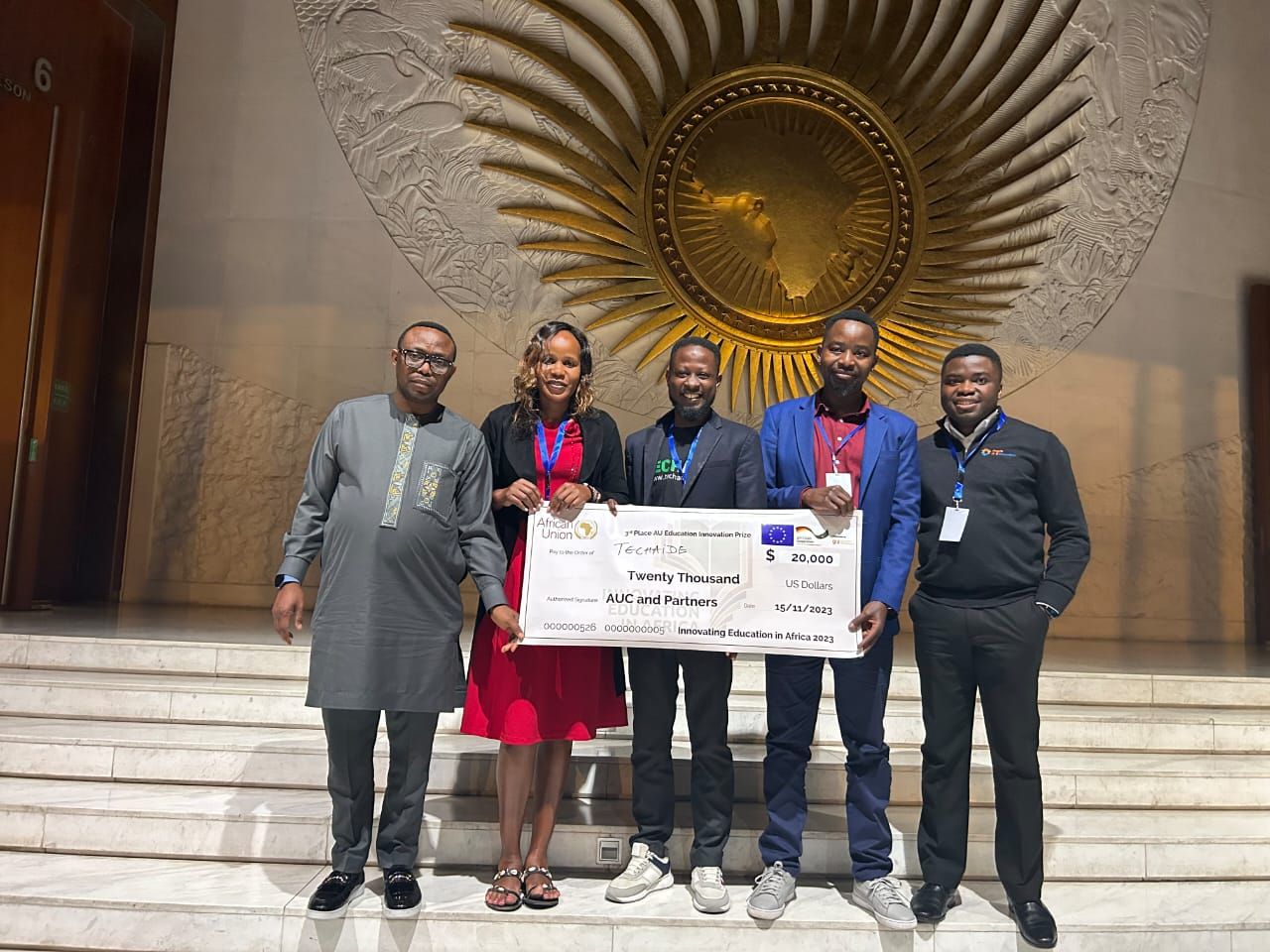
TECHAiDE Makes Ghana Proud at African Union Commission- Innovating Education in Africa (AUC IEA) 2023 Pitch Event in Ethiopia.
TECHAiDE emerged as a winner at the recent AUC IEA EdTech event held in Addis Ababa, Ethiopia. This victory not only highlights the innovative spirit of TECHAiDE but also brings immense pride to Ghana.